Setting up the Edge Device
Create an AWS Greengrass Group
This section describes how to configure the EC2-based Greengrass gateway that will host the lambdas for reading drilling data as well as making predictions later on. To start this process, switch to the IoT Core service (Click “Services” at the top right corner, enter “iot” in the search bar and select “IoT Core”). If you have never used IoT core before, click “Get started” on the following screen:

Prior to deploying Greengrass, IoT Core needs to be configured accordingly. IoT Core offers a wizard to do this. To access the wizard, please click “Greengrass” on the left-hand menu:
When you see the screen “Welcome to AWS Greengrass” click on the left button named “Get Started” or click “Create Group” as shown below. This will start a wizard for the creation of a Greengrass Core.
- Use the default creation

- Provide a name for the group such as “DrillGateway” (no spaces)
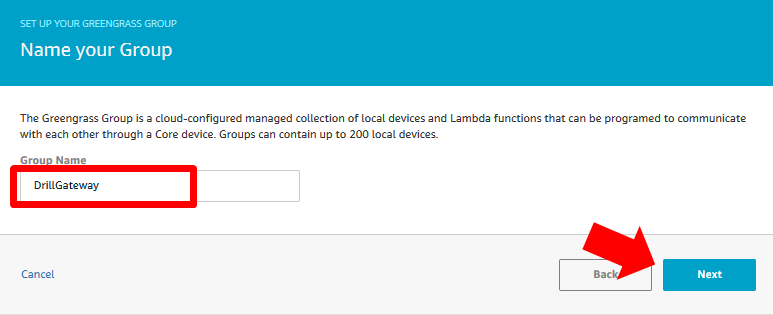
- Leave the name of the core as it is proposed and all other parameters as suggested by the wizard

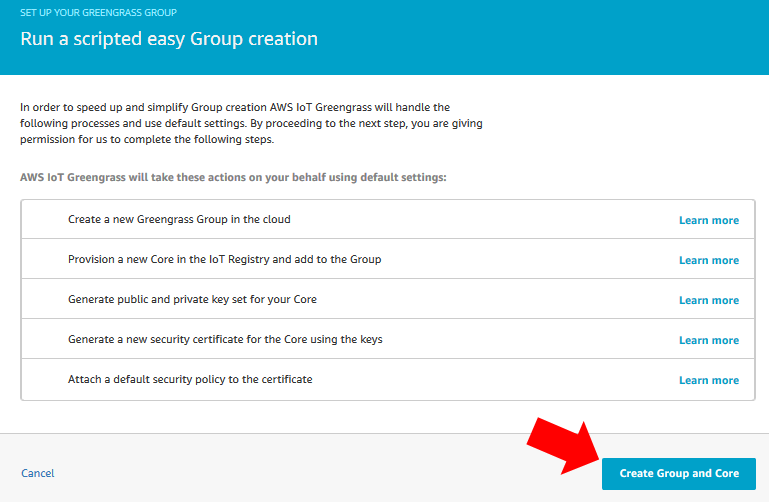
The wizard will show a summary screen as shown below before automatically creating a set of certificates and registering them with the GG core. On this screen, click “Create Group and Core”:
Note: If you encounter an error stating “resource already exists” this means that you already have created a thing with the given name. There are two options to fix this:
- Provide a different name for you GG core, e.g., if you tried “DrillGateway” then appending a number such as “DrillGateway2” may help
- Cancel the wizard, go to “Manage” and then “Things” to delete the conflicting entry in the device registry of IoT Core. You can do this by selecting “...” at the top right corner of the thing and then clicking “Delete”.
Finally, the wizard will allow you to download the configuration file as well as a set of certificates for your GG core. Click on “Download the resources as tar.gz”and store the downloaded file on anywhere your local hard disk.

Typically, it is required to download the GG release you want to you for the chip architecture of the device you are using. In this case, we can skip this (the proper GG release has been already installed by the CloudFormation template). Thus, to finish this step, please click “Finish” at the bottom of the screen.

Note: It is very important to click “Finish” here as the final registration of the different components (certificates, things...) only happens during this step. If you forget to click “Finish” here, it will result in GG not being properly set up. This can only be fixed by deleting the thing manually.
The wizard is finished properly, if it shows the GG core as follows:
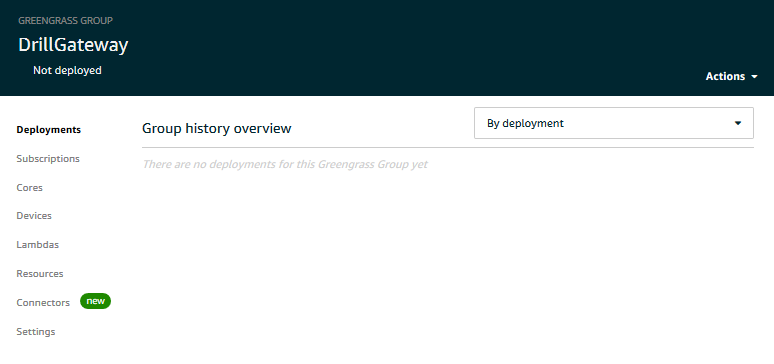
It is recommended that you keep a browser tab with this screen open and complete the following steps in a new browser tab.
Configure the AWS Greengrass Device
AWS Greengrass will be running on EC2 within an AWS Cloud9 environment. With this it is possible to work on the instance (having a shell terminal and be able to upload/change files easily) and only requires a browser.
Open AWS Cloud9 from the AWS Console
Select “Open IDE” on the newly created environment:
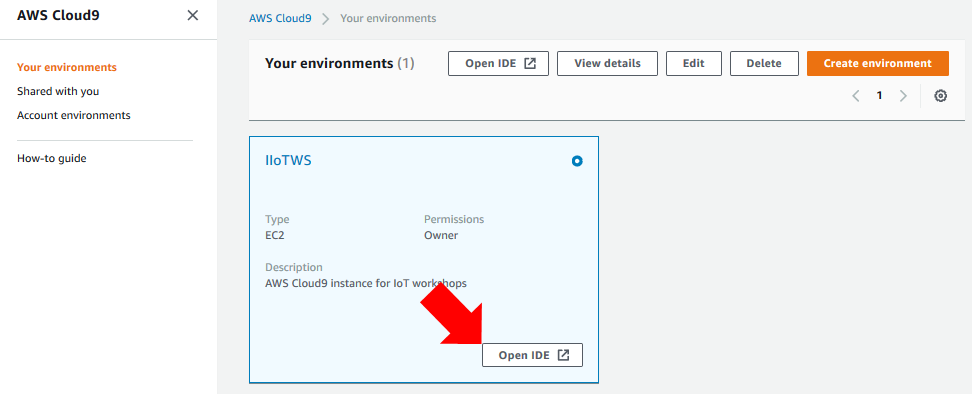
Note: If there is no Cloud9 instance listed in your account, it is likely that you have been using a login to your account that uses the “AssumeRole” / Switch Role functionality. This creates issues with Cloud9 and we recommend directly logging into the Account without using “AssumeRole” / Switch Role.
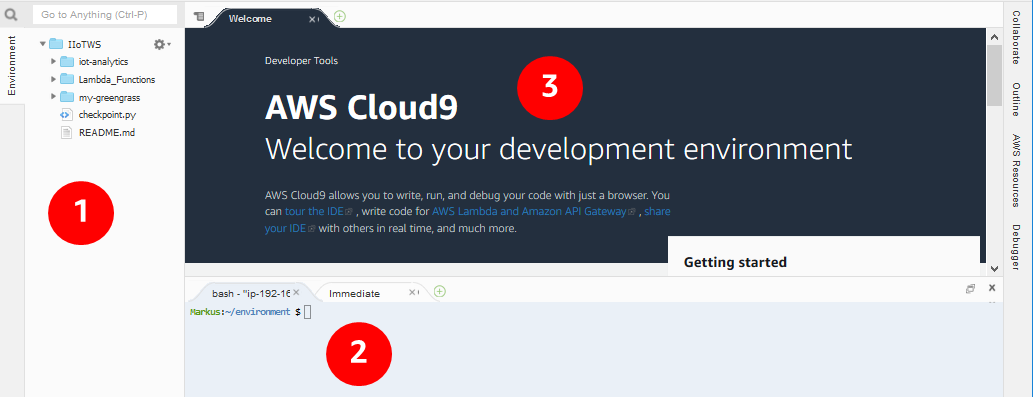
Cloud9 will open a new browser tab and show the following start screen with several elements:
- File Explorer that shows which files are part of your development project
- Console window that provides you with console access to the EC2 instance running Cloud9.
- Code development and editing area.
For any changes made to files in this area, it has to be noted that they need to be saved by pressing CTRL+S or File → Save.
All console commands in the following have to be entered in the console window.
Upload the Greengrass setup configuration:
- Select the Directory “my-greengrass”
- Click on “Upload Files...” in the editing area (#3 in the screenshot above)
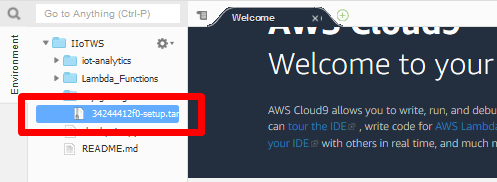
- Select the resource file ending in “-setup.tar.gz” that was downloaded during the Greengrass setup, e.g., “34244412f0-setup.tar.gz”. The leading string is the identifier of the thing associated with the Greengras
Once the upload is finished, the file explorer will show the file similar to the following:
Configure and Start the AWS Greengrass software
In the AWS Cloud9 terminal type in
sudo tar -xzvf ~/environment/my-greengrass/*-setup.tar.gz -C /greengrass
sudo /greengrass/ggc/core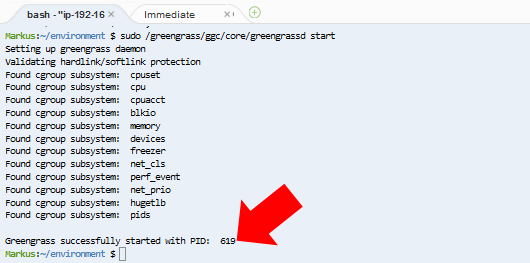
Greengrass has been started successfully, if the console window shows a message similar to the one above.
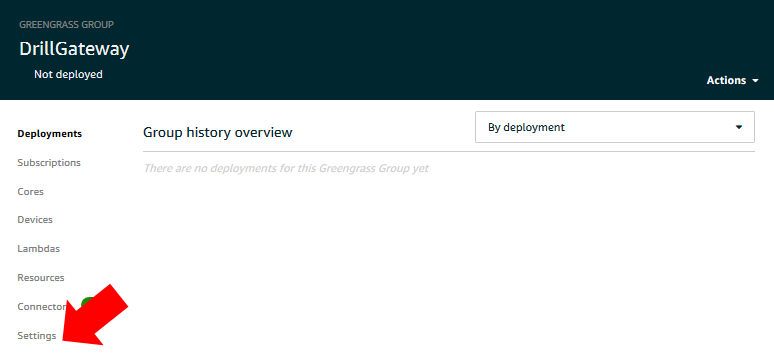
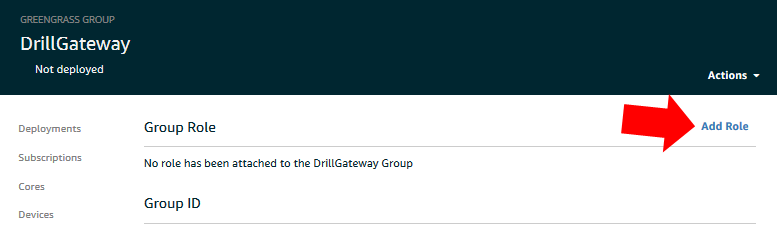
Keep the Cloud9 tab open and switch back to the GG tab that we used for registering AWS Greengrass. If you closed the tab, go back to IoT Core and then go back to the AWS Greengrass Console. As a first step, the AWS Greengrass group must be enabled to access AWS services (upload logs to CloudWatch, download files like the ML model etc.).
Hence, open the “Settings” tab of the GG group.
First, we need to assign a role to the Greengrass group, so that it can access AWS resources. To do so, click “Add roles”. This is the same mechanism that is used for instance in cases where EC2 instances have to access other AWS services.
The role has been properly configured by the CloudFormation template (it is possible to view it in IAM). The next screen will show a list of roles that can be associated with AWS Greengrass groups. Select the one starting with “IIoTWS-GG-GatewayRole” and click “Save”:

Note: if there are multiple options for selecting a role, select any role that starts has “GGGatewayRole” in the middle as shown in the screenshot above. This may occur because the account already has roles configured for Greengrass. In this case, please use IAM to ensure that the selected role has the policies “AmazonS3ReadOnlyAccess” and “AWSGreengrassResourceAccessRolePolicy”.
The screen will return to the Settings page and show the associated role along with the policies that are now in place for the AWS Greengrass group:

Finally, we also want our AWS Greengrass group to store logs locally for debugging and monitoring purposes. Note that the configuration to send logs to CloudWatch is also here and can be added optionally in a similar way:
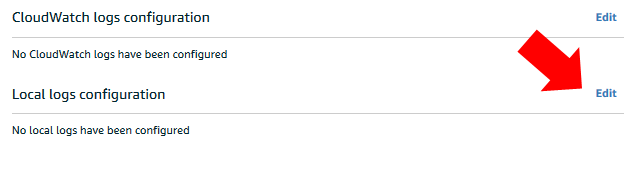
- Go down to “Local logs configuration” and click on “Edit”
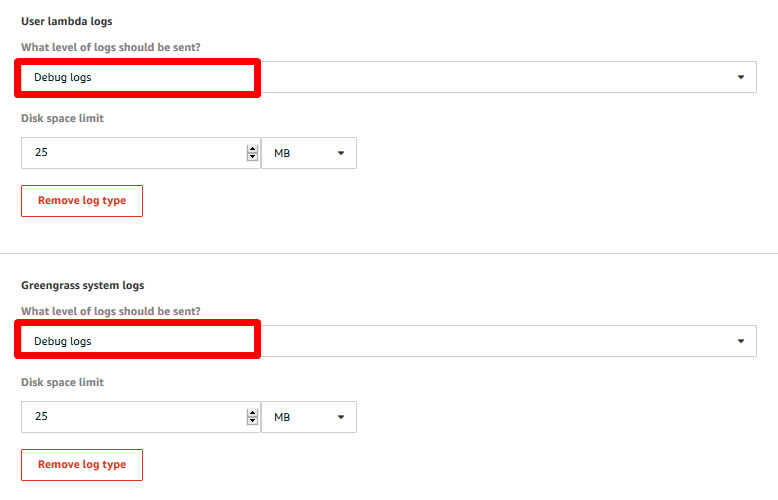
- Click “Add another log type”

- Select “User Lambdas” and “Greengrass system”
- Click Update

- select level as “Debug” for both log types
- Leave the other values as they are.
- click “Save” at the bottom of the screen.
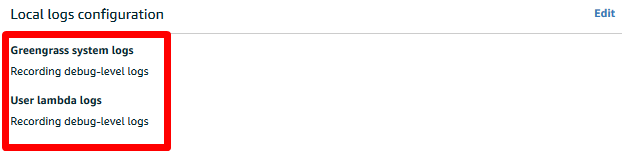
The “Settings” will now show the logs configuration as follows:
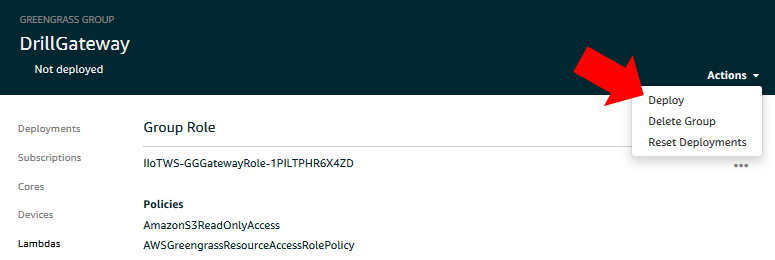
We can now make an initial deployment of the AWS Greengrass group as follows:
- Click on “Actions” → “Deploy”
- When asked for “Configure how Devices discover your Core” select “Automatic detection”
- When asked for “Grant permission to access other services” select “Grant permission”
If the account previously has not been used with AWS Greengrass, the deployment can potentially fail because AWS Greengrass cannot assume the service role required to execute the deployment.

Please go to AWS Cloud9 in the terminal and type the following command
gg_service_arn=$(aws iam get-role --role-name Greengrass_ServiceRole --query Role.Arn)
aws greengrass associate-service-role-to-account --role-arn ${gg_service_arn//\"/}
The output on the console should look similar to the following:

Finally, redeploy with “Actions” → “Deploy” in the AWS Greengrass console tab. The indicator below the AWS Greengrass group name should turn green and read “Successfully completed”.

